计算理论导论代写 CSC236H代写 LaTeX代写 计算机作业代写
634CSC236H-Assignment 1 计算理论导论代写 • For this assignment, you must work individually, produce a PDF file named a1.pdf, and submit it to MarkUs. Submissions must be typed. • For this ass...
View detailsSearch the whole station
计算机网络代做 Problem 1 (0.5 pt each, no partial credit) Carefully read the following statements. If the statement includes incorrect information,
Due: Tuesday, March 8 at 6 PM (BEFORE CLASS)
No late submission will be accpted to go through solutions during the class on the due date.
A submission must be made as a PDF file on Canvas.
Carefully read the following statements. If the statement includes incorrect information, explain why it is wrong in one or two sentences. Otherwise, write “True.”
Problem 1.1
File Transfer Protocol has two modes: Active and Passive. When using the passive mode, a FTP client needs to initiate the data transfer channel with port 21.
Problem 1.2
A socket is a programing interface that provides data transfer as a service for a user application.
To identify the user application, it uses a port number and the host’s MAC address.
Consider a packet which begins at end system A and travels over three links to a destination end system. These three links are connected by two packet switches.
Suppose now the packet is 1,200 bytes, the propagation speed on all three links is 2.5 × 100 km/s, the transmission rates of all three links are 10 Mbps (bps: bits per second), the packet switch processing delay is 4 msec, the length of the first link is 3,000 m, the length of the second link is 4,000 m, and the length of the last link is 2,000 m. For these values, what is the end-to-end delay assuming no queuing delays?
Problem 3.1 (0.5 pt)
Compute the 16-bit UDP checksum of a message consisting of the following two strings: 0110 0011 1010 1010 and 1100 0101 0010 0111.
Problem 3.2 (0.5 pt)
Let’s consider 4-bit checksum for simplicity. (Note that although UDP uses 16-bit words in computing the checksum, for this problem you are being asked to consider 4-bit sums.)
Alice sent a segment that contains three 4-bit strings: 0100, 0011, and 1111.
Bob received the segment and confirmed the 4-bit checksum is correct. However, the segment had actually experienced some bit flips. Find a minimal example of such bit flips that was not detected by the checksum. (Here, “minimal” means the least number of bit flips.)
Problem 4.1
Consider a datagram network with the network address 10.5.0.128/25. Suppose a router uses longest prefix matching (of the host part) and has the following forwarding table:
| Prefix Match | Interface |
| 0000 1010.0000 0101.0000 0000.101 | 0 |
| 0000 1010.0000 0101.0000 0000.1011 | 1 |
| 0000 1010.0000 0101.0000 0000.110 | 2 |
Problem 4.1.1 (0.4 pt each, total 1.2 pt)
For each of the three interfaces, give the associated range of destination host addresses.
Problem 4.1.2 (0.2 pt each, total 0.6 pt)
For a subnet with each prefix, answer the number of user devices that can be accommodated.
Problem 4.2 (0.7 pt)
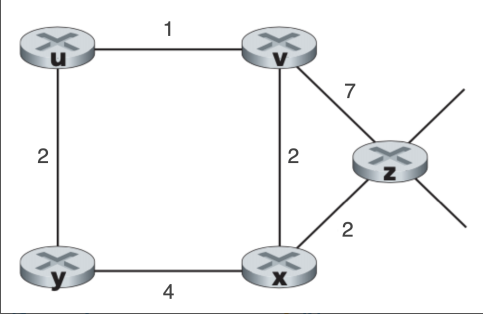
Consider the network shown below, and assume that each node initially knows the costs to each of its neighbors. Consider the distance-vector algorithm and show the distance table entries at node z (Show each step).
更多代写:美国cs抄作业被发现 托福代考多少钱 英国Econometrics计量经济学代上网课 Dissertations代写 Common Application文书代写 计算机网络课业代做
合作平台:essay代写 论文代写 写手招聘 英国留学生代写
CSC236H-Assignment 1 计算理论导论代写 • For this assignment, you must work individually, produce a PDF file named a1.pdf, and submit it to MarkUs. Submissions must be typed. • For this ass...
View detailsCSC 165 H1 Term Test 3 — Question 1 of 4 计算机科学的数学表达与推理代写 Aids Allowed: Your own notes taken during lectures and office hours, the lecture slides and recordings (for all secti...
View details网网络代写现象很多么?学生为啥都在找计算机网络代写 ? 留学生网络代写 网络代写其实在很久以前就有了,说起来的话,就算是在古时候没有网络的情况下,求学的书生们当中依然存在这种情况,只不过需求较少,...
View detailsCSCI-UA.0480-009 midterm (47 points) 计算机网络代写 1. (3 points) What are the units of throughput, queueing delay, window size, capacity, RTT, and Bandwidth-Delay Product? Instructi...
View details