代考人工智能考试 Artificial Intelligence代考 AI代考 CS代考
198Artificial Intelligence: Sample Mid-Term Exam 代考人工智能考试 Problem 1 The following problem is known as EXACT SET COVER: You are given a universal set U of elements and a collection W of su...
View detailsSearch the whole station
信息安全考试代考 13 QUESTIONS (60 MARKS – 120 minutes) Answer all questions in the answer booklets This question paper will NOT be present during marking and
13 QUESTIONS (60 MARKS – 120 minutes)
Answer all questions in the answer booklets
This question paper will NOT be present during marking and will be destroyed.
Any writing on this question paper will not be considered for assessment.
Describe three important information assets you would want to secure in any typical commercial organisation you may work with in the future. Ensure you describe why the security of each of these information assets is important.
Explain the difference between quantitative risk analysis and qualitative risk analysis.
Describe the original purpose of the “sticky bit” in Unix executable file permissions. To what extent is this used in for executable files in Linux systems? Describe the difference in behaviour when a Linux directory does and does not have the sticky bit set.
Explain whether you would consider the need for the use of an electronic proximity card (similar to a Translink “GO-card”) and a separate lock needing a physical key, as two-factor authentication to gain physical access to a secure rack in a data centre?
The MD5 and SHA-1 cryptographic one-way hash functions are no longer considered secure for a number of cryptographic applications. Explain for each of MD5 and SHA-1 the current status of their preimage resistance, second-preimage resistance and collision resistance. Explain what general cryptographic applications you could still currently rely on each of MD5 and SHA-1 and why you could still rely on these algorithms in those situations.
What are the possible output sizes for the BLAKE cryptographic one-way hash function?
A biometric system has the following parameters: FRR = 0.03, FAR = 0.05. We further know that in 98% of all cases, genuine users are trying to use the system, and in 2% of the cases we have an impostor trying to circumvent the system.
Given the system has accepted a user, what is the probability that this user is genuine and not an impostor? (You should carry at least four significant figures in all calculations to avoid errors.)
The following ciphertext:
“ULXWMVQRSVCZNKLWMVQDSZRWMVQLSV”
was produced with a Vigenère cipher using only one of the following 20 keys: PRIME SHE AN GUY TEN FAR MOTOR BUY CIPHER KNIGHT BIKE FRED TOOLS BAKER BY HEROES EXTEND MIGHT ELF LOCAL.
a) [7 marks] Demonstrate the most efficient method to decrypt the ciphertext with only the resources you have available to you in this examination.
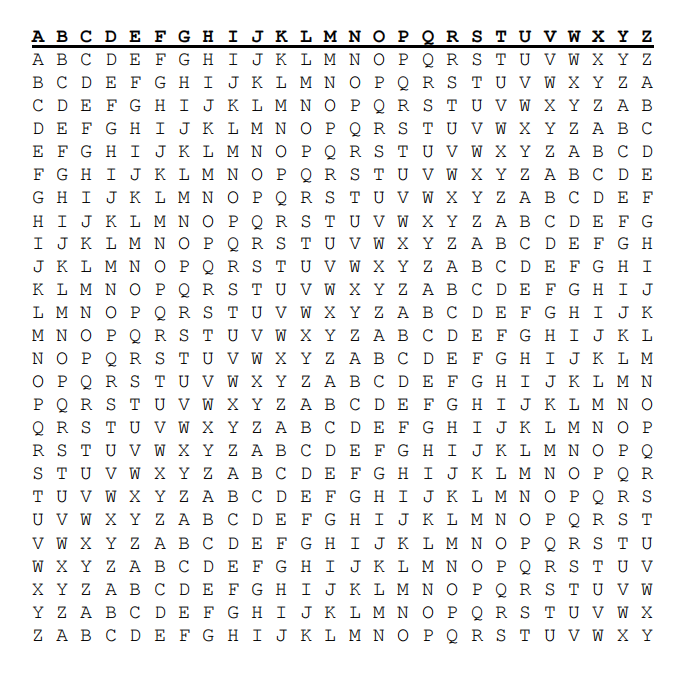
b) [5 marks] Correctly decrypt the ciphertext using any method. A Vigenère table is provided below.
Outline the process required to validate an X.509 version 3 digital certificate, including:
a) the components of each certificate that are processed and how they are checked for authenticity and integrity;
b) all intermediate certificates in a chain; and
c) checking revocation.
Describe when and how nonces are used in the TLS handshake.
Describe and explain the difference between signature-based detection and anomaly-detection in IDS and IPS?
Alice and Bob are using the Diffie-Hellman protocol to establish a shared secret key.
They agree on the public parameters n = p = 11 and a generator a = g = 3.
Alice chooses a random number x=3 and Bob chooses a random number y=4.
Show the computations performed by Alice and Bob to each compute the shared secret key that will be established between them.
WPA and WPA2 Pre-Shared Keys may be entered as either the 64 hexadecimal characters for the actual binary key or otherwise as a passphrase of 8± 63 (but not 64) printable ASCII characters which are then hashed using the SSID as the salt and 4096 rounds of HMAC-SHA1.
a) [1 mark] How many bits are in a 64 hexadecimal character key?
b) [1 mark] What is the total entropy of a truly random 64 hexadecimal character key?
c) [1 mark] How many bits are in 63 printable ASCII characters? (There are 95 possible different printable ASCII characters.)
d) [2 marks] What is the total entropy of 63 truly random printable ASCII characters?
e) [3 marks] What is the total entropy of an English phrase of 63 printable ASCII characters?
更多代写:语言学作业代写 ielts indicator作弊 英国艺术类作业代做 艺术类essay代写 医学英文论文写作 美国作业抄袭
合作平台:essay代写 论文代写 写手招聘 英国留学生代写
Artificial Intelligence: Sample Mid-Term Exam 代考人工智能考试 Problem 1 The following problem is known as EXACT SET COVER: You are given a universal set U of elements and a collection W of su...
View details